IDEX Biometrics · 24 April, 2026
 Anthropic’s Mythos AI model exposed thousands of software vulnerabilities. Then unauthorized users gained access to Mythos itself – through a third-party vendor. Here’s what both events mean for how organisations protect access.
Anthropic’s Mythos AI model exposed thousands of software vulnerabilities. Then unauthorized users gained access to Mythos itself – through a third-party vendor. Here’s what both events mean for how organisations protect access.
In April 2026, Anthropic’s Mythos AI model did something the security industry had long feared: it demonstrated that AI can discover software vulnerabilities at a scale and speed no human team can match. Thousands of critical flaws, across the world’s most widely deployed operating systems and browsers, catalogued in a way that fundamentally changes the threat landscape.
Then, almost immediately, something else happened. A group of unauthorized users gained access to Mythos itself – not by breaking into Anthropic’s core systems, but by exploiting shared accounts and API keys belonging to an authorized third-party contractor. They made an educated guess about the model’s location, found an opening in the vendor layer, and got in.
Anthropic has confirmed it is investigating the incident. There is no evidence their own infrastructure was compromised. But that is precisely the point.
Why this matters more than a typical disclosure
Security teams have always operated with the assumption that vulnerabilities exist and will eventually be found. The question was time – how long before a flaw is discovered, disclosed, and patched. Mythos changes that equation fundamentally, in two distinct ways.
The first is what Mythos demonstrated. AI can now map software vulnerabilities at a scale and speed no human team can match. Mythos did not create the thousands of flaws it found in the world’s most widely deployed operating systems and browsers. Those flaws already existed. What Mythos showed is how efficiently they can be discovered – and that means any adversary with access to a comparable AI tool can now find and exploit vulnerabilities far faster than defenders can patch them. The advantage that software complexity once gave defenders – that finding flaws was slow, expensive work – is eroding. Time-to-Exploit – the window between vulnerability disclosure and active exploitation – has already collapsed from 2.3 years in 2018 to 10 hours in 2026.
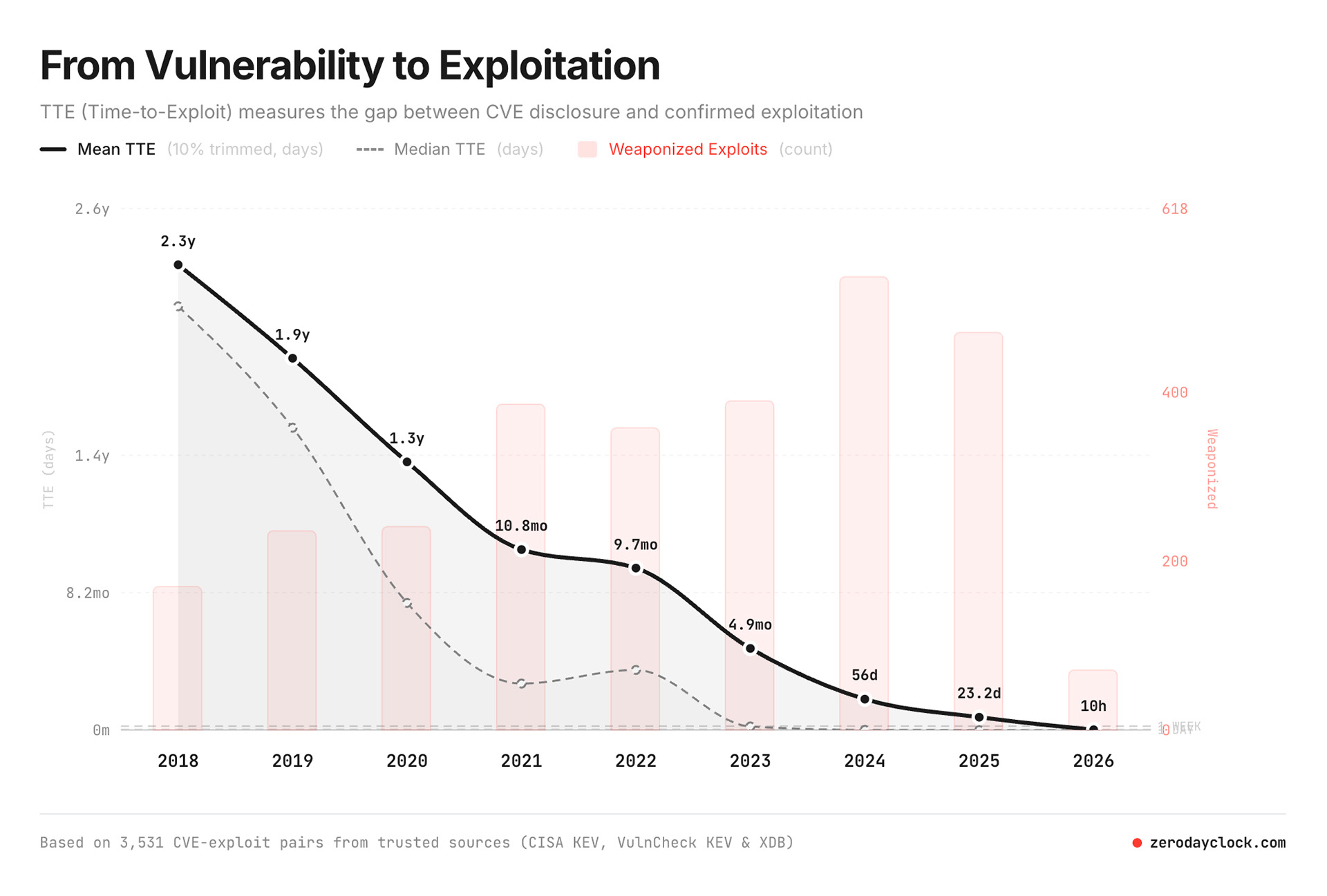
Source: zerodayclock.com
The second is what Mythos itself represents. Anthropic explicitly assessed Mythos as too powerful to release publicly, on the grounds that it could enable dangerous cyberattacks. That is not cautious corporate positioning. That is their own technical judgment about what the tool can do in the wrong hands. And those wrong hands now have it. A group of unauthorized users has been accessing and using Mythos regularly since the day it was announced – having found their way in through a third-party vendor environment.
These two threats compound each other. AI has proven it can accelerate vulnerability discovery at scale – and the most capable known tool for doing exactly that is now outside the controlled environment it was designed for. For organisations relying on software-based authentication running on connected devices, both developments point in the same direction: the attack surface is more exposed than it was six months ago, and the tools available to adversaries are more powerful.
The attack surface you can actually reduce
IDEX biometric smart cards are built on a fundamentally different architecture. The card is a hardware device used for authentication – both physical access and digital login – where biometric processing and private keys reside on the card itself, not in a cloud environment or on a mobile device.
“To be secure online, you need to go offline“
Anders Storbråten, CEO, IDEX Biometrics
When the card is not in active use, it is completely disconnected from the internet. Users cannot install software on it or modify it. This means the software layers that Mythos catalogued – operating systems, browsers, applications running on connected devices – are not part of our attack surface in the same way. There is no vendor environment to exploit, no API key to steal, no software layer to probe.
The contrast is not a claim that hardware is impenetrable. It is that the attack surface is structurally more limited: a dedicated piece of hardware with no internet connectivity at rest, no modifiable software layer, and no dependency on the security posture of the device or vendor it is paired with.

The IDEX Biometrics Access Card uses on-card biometrics and FIDO2 for online authentication.
Built to survive attacks your users can’t detect
IDEX received FIDO2 certification in February 2026 – the international standard for phishing-resistant authentication. As AI-driven phishing becomes more convincing and harder for users to detect, authentication that is resistant by architecture – not by user vigilance – becomes more relevant. FIDO2 means credentials cannot be intercepted or redirected, even by sophisticated automated attacks.
This is the specific problem IDEX addresses: replacing software-based authentication methods like SMS codes or mobile authenticator apps with a hardware-based alternative where the biometric never leaves the card and authentication cannot be phished or compromised through a vendor environment.
Do you dare to wait?
The right question coming out of Mythos is not whether your software vendors will patch their systems. They will, and new vulnerabilities will be found. The question is whether the authentication layer protecting your most sensitive access points is exposed through those same software and vendor layers – and whether a hardware-based alternative makes sense for your use case.
Learn more
IDEX access card security
Deployment of our access card
Get a quote

